
20411B-ENU-TrainerHandbook
.pdf
7-10 Configuring and Troubleshooting Remote Access
Lesson 2 |
MCT |
|
Configuring VPN Access |
||
|
Lesson Objectives |
USE |
|||
|
||||
After completing this lesson, you will be able to: |
.ONLY |
|||
• Describe what a VPN connection is, and how it is used to connect remote network clients. |
||||
• Describe the tunneling protocols used for a VPN connection. |
||||
• |
Describe VPN Reconnect. |
|||
• Describe configuration requirements for a VPN connection. |
||||
• |
Explain how to configure VPN access. |
|||
|
||||
• Describe additional tasks that you can be completed after configuring a VPN server. |
|
|||
• Describe the features in and benefits of the Connection Manager Administration Kit. |
|
|||
• Explain how to create a connection profile using the Connection Manager Administration Kit. |
STUDENT |
|||
What Is a VPN Connection? |
||||
To emulate a point-to-point link, data is |
|
|||
|
||||
encapsulated (or wrapped) and prefixed with a |
|
|||
header; this header provides routing information |
|
|||
that enables the data to traverse the shared or |
|
|||
|
|
|
||
public network to reach its endpoint. |
|
USE |
||
To emulate a private link, data is encrypted |
|
|||
to ensure confidentiality. Packets that are |
|
|||
intercepted on the shared or public network are |
|
|||
indecipherable without encryption keys. The link |
|
|||
in which the private data is encapsulated and |
|
|||
|
|
|||
encrypted is known as a VPN connection. |
|
|
||
|
|
|
||
There are two types of VPN connections: |
PROHIBITED |
|||
• |
Remote access |
|||
To properly implement and support a VPN environment within your organization, it is important that you understand how to select a suitable tunneling protocol, how to configure VPN authentication, and how to configure the Network Policy and Access Services server role to support your chosen configuration.
• Site-to-site
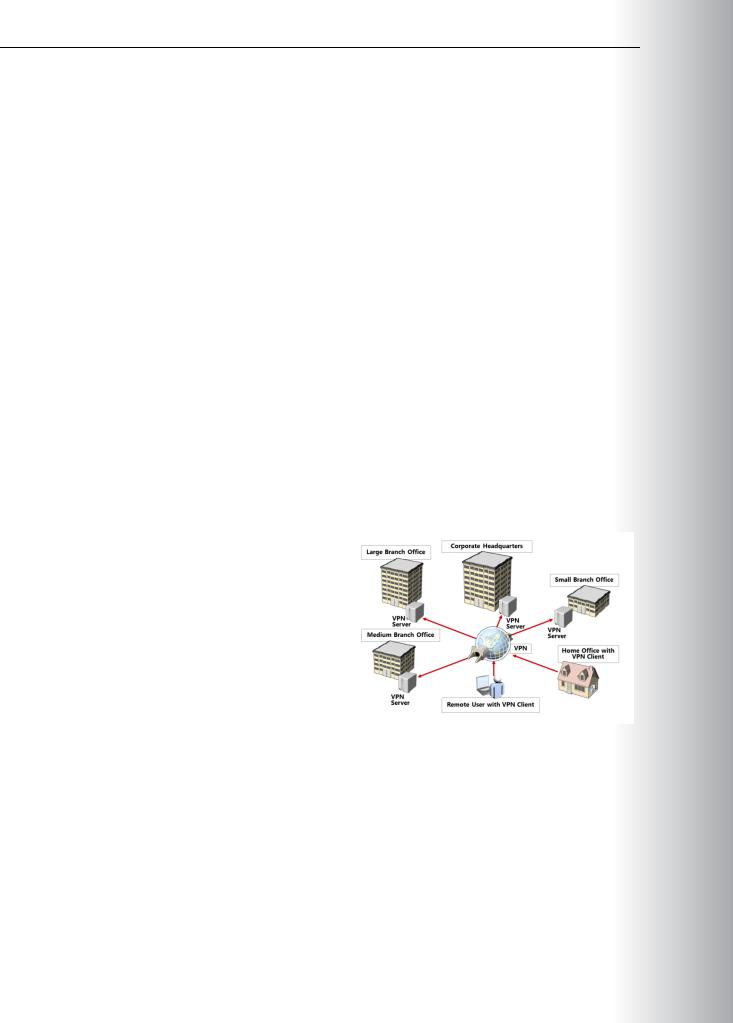
Remote Access VPN
Remote access VPN connections enable your users who are working offsite (for example, at home, at a customer site, or from a public wireless access point) to access a server on your organization’s private network using the infrastructure that a public network provides, such as the Internet. From the user’s perspective, the VPN is a point-to-point connection between the computer, the VPN client, and your organization’s server. The exact infrastructure of the shared or public network is irrelevant because it appears logically as if the data is sent over a dedicated private link.

Administering Windows Server® 2012 7-11
Site-to-Site VPN
Site-to-site VPN connections, which are also known as router-to-router VPN connections, enable your |
MCT |
|
organization to have routed connections between separate offices (or with other organizations) over a |
||
|
||
public network while helping to maintain secure communications. A routed VPN connection across the |
|
|
Internet logically operates as a dedicated WAN link. When networks connect over the Internet, a router |
|
|
forwards packets to another router across a VPN connection. To the routers, the VPN connection operates |
||
as a data-link layer link. |
USE |
|
|
||
A site-to-site VPN connection connects two portions of a private network. The VPN server provides a routed connection to the network to which the VPN server is attached. The calling router (the VPN client)
authenticates itself to the answering router (the VPN server), and for mutual authentication, the answeringONLY router authenticates itself to the calling router. In a site-to site VPN connection, the packets sent from
either router across the VPN connection typically do not originate at the routers.
VPN connections that use the Point-to-Point Tunneling Protocol (PPTP), Layer 2 Tunneling Protocol with Internet Protocol Security (L2TP/IPsec), and Secure Socket Tunneling Protocol (SSTP), have the following. properties:
• Encapsulation. With VPN technology, private data is encapsulated with a header containing routing information that allows the data to traverse the transit network.
• Authentication. Authentication for VPN connections takes the following three different forms:
o User-level authentication by using Point-to-Point Protocol (PPP) authentication. To establish the VPN connection, the VPN server authenticates the VPN client that is attempting the connection by using a PPP user-level authentication method, and verifies that the VPN client has the appropriate authorization. If you use mutual authentication, the VPN client also authenticates the VPN server, which provides protection against computers that are masquerading as VPN servers.
o Computer-level authentication by using Internet Key Exchange (IKE). To establish an IPsec |
|
security association, the VPN client and the VPN server use the IKE protocol to exchange either |
|
|
STUDENT |
computer certificates or a pre-shared key. In either case, the VPN client and server authenticate |
|
each other at the computer level. We recommend computer-certificate authentication becauseUSEit is a much stronger authentication method. Computer-level authentication is only performed for L2TP/IPsec connections.
o Data origin authentication and data integrity. To verify that the data sent on the VPN connection originated at the other end of the connection and was not modified in transit, the data contains a
•
cryptographic checksum based on an encryption key known only to the sender and the receiver. PROHIBITED
Data origin authentication and data integrity are only available for L2TP/IPsec connections.
Packets that are intercepted in the transit network are unintelligible to anyone who does not have the common encryption key. The encryption key’s length is an important security parameter. You can use computational techniques to determine the encryption key. However, such techniques require more computing power and computational time as the encryption keys get larger. Therefore, it is important to use the largest possible key size to ensure data confidentiality.


|
Administering Windows Server® 2012 7-13 |
|
SSTP |
MCT |
|
|
|
|
SSTP is a tunneling protocol that uses the HTTP/Secure (HTTPS) protocol over TCP port 443 to pass traffic through firewalls and web proxies, which otherwise might block PPTP and L2TP/IPsec traffic. SSTP
provides a mechanism to encapsulate PPP traffic over the Secure Sockets Layer (SSL) channel of the HTTPS protocol. The use of PPP allows support for strong authentication methods, such as EAP-TLS. SSL provides
transport-level security with enhanced key negotiation, encryption, and integrity checking. |
USE |
|
|
When a client tries to establish a SSTP-based VPN connection, SSTP first establishes a bidirectional HTTPS |
|
layer with the SSTP server. Over this HTTPS layer, the protocol packets flow as the data payload using the |
|
following encapsulation and encryption methods: |
|
• Encapsulation. SSTP encapsulates PPP frames in IP datagrams for transmission over the network. SSTP |
|
uses a TCP connection (over port 443) for tunnel management and as PPP data frames. |
|
• Encryption. The SSTP message is encrypted with the SSL channel of the HTTPS protocol. |
|
IKEv2 ONLY
IKEv2 uses the IPsec Tunnel Mode protocol over UDP port 500. IKEv2 supports mobility making it a good. protocol choice for a mobile workforce. IKEv2-based VPNs enable users to move easily between wireless hotspots, or between wireless and wired connections.
The use of IKEv2 and IPsec enables support for strong authentication and encryption methods. |
STUDENT |
||
• Encapsulation. IKEv2 encapsulates datagrams by using IPsec ESP or Authentication Header (AH) for |
|||
transmission over the network. |
|||
• Encryption. The message is encrypted with one of the following protocols by using encryption keys |
|||
that are generated from the IKEv2 negotiation process: AES 256, AES 192, AES 128, and 3DES |
|||
encryption algorithms. |
|||
IKEv2 is supported only on computers that are running Windows 7, Windows 8, Windows Server 2008 R2, |
|||
and Windows Server 2012. IKEv2 is the default VPN tunneling protocol in Windows 7 and Windows 8. |
|
|
|
What Is VPN Reconnect? |
|
USE |
|
In dynamic business scenarios, users must be able |
|
|
|
|
|
||
to securely access data anytime, from anywhere, |
|
|
|
and access it continuously, without interruption. |
|
|
|
|
|
|
|
For example, users might want to securely access |
|
|
|
data that is on the company’s server, from a |
|
|
|
branch office or while on the road. |
|
|
|
To meet this requirement, you can configure |
|
|
|
the VPN Reconnect feature that is available in |
|
|
|
Windows Server 2012, Windows Server 2008 R2, |
|
|
|
Windows 8, and Windows 7. With this feature, |
|
|
|
users can access the company’s data by using |
|
|
|
a VPN connection, which will reconnect |
|
|
|
|
|
|
|
automatically if connectivity is interrupted. VPN Reconnect also enables roaming between different |
|
|
|
networks. |
|
|
|
a laptop that is running Windows 8. When the user travels to work in a train, he or she connects to the Internet with a wireless mobile broadband card, and then establishes a VPN connection to the company’s network. When the train passes through a tunnel, the Internet connection is lost. After the train emerges
VPN Reconnect uses the IKEv2 technology to provide seamless and consistent VPN connectivity. Users PROHIBITED who connect via a wireless mobile broadband will benefit most from this capability. Consider a user with

7-14 Configuring and Troubleshooting Remote Access |
MCT |
|
|
|
|
|
|
|
from the tunnel, the wireless mobile broadband card reconnects automatically to the Internet. With older versions of Windows client and server operating systems, VPN did not reconnect automatically. Therefore,
the user would have to repeat the multistep process of connecting to the VPN manually. This was time- |
USE |
|
consuming and frustrating for mobile users with intermittent connectivity. |
||
With VPN Reconnect, Windows Server 2012 and Windows 8 re-establish active VPN connections |
||
|
automatically when Internet connectivity is re-established. Even though the reconnection might take several seconds, users need not reinstate the connection manually, or authenticate again to access internal network resources.
The system requirements for using the VPN Reconnect feature are as follows:
• |
.ONLY |
Windows Server 2008 R2 or Windows Server 2012 as a VPN server. |
|
• Windows 7, Windows 8, Windows Server 2008 R2, or Windows Server 2012 client. |
|
• |
Public Key Infrastructure PKI, because a computer certificate is required for a remote connection with |
|
VPN Reconnect. You can use certificates issued by either an internal or public CA. |
•Your VPN server requires two network  STUDENT interfaces. You must determine which
STUDENT interfaces. You must determine which
network interface will connect to the Internet, and which network interface will connect to your private network. During configuration, you will be asked to choose which network interface connects to the Internet. If you
specify the incorrect interface, your remote
access VPN server will not operate correctly. USE
•Determine whether remote clients receive IP addresses from a DHCP server on your private network or from the remote access VPN server that you are configuring. If you have a DHCP server on your private network, the remote access VPN server can lease 10 addresses at a time from the DHCP
server, and then assign those addresses to remote clients. If you do not have a DHCP server on your
private network, the remote access VPN server can automatically generate and assign IP addresses to PROHIBITED remote clients. If you want the remote access VPN server to assign IP addresses from a range that you
specify, you must determine what that range should be.
•Determine whether you want connection requests from VPN clients to be authenticated by a RADIUS server or by the remote access VPN server that you are configuring. Adding a RADIUS server is useful if you plan to install multiple remote access VPN servers, wireless access points, or other RADIUS clients to your private network.

|
Administering Windows Server® 2012 |
MCT |
||
|
7-15 |
|
||
• |
Determine whether VPN clients can send DHCPINFORM messages to the DHCP server on your private |
|||
|
network. If a DHCP server is on the same subnet as your remote access VPN server, DHCPINFORM |
|
|
|
|
messages from VPN clients will be able to reach the DHCP server after the VPN connection is |
|
|
|
|
established. If a DHCP server is on a different subnet from your remote access VPN server, make sure |
|||
|
that the router between subnets can relay DHCP messages between clients and the server. If your |
USE |
||
|
|
|
||
|
router is running Windows Server 2008 R2 or Windows Server 2012, you can configure the DHCP |
|
|
|
|
Relay Agent service on the router to forward DHCPINFORM messages between subnets. |
|
|
|
• |
Ensure that the person who is responsible for the deployment of your VPN solution has the necessary |
|||
|
administrative group memberships to install the server roles and configure the necessary services; |
.ONLY |
||
|
membership of the local Administrators group is required to perform these tasks. |
|||
|
|
|
||
Demonstration: How to Configure VPN Access |
|
|
||
This demonstration shows how to: |
|
|
||
• |
Configure Remote Access as a VPN server. |
STUDENT |
||
• |
Configure a VPN client. |
|||
|
|
|||
Demonstration Steps |
|
|
||
Configure Remote Access as a VPN server |
|
|
||
1. |
Sign in to LON-RTR as Adatum\Administrator with the password Pa$$w0rd. |
|
|
|
2. |
On LON-RTR, open Server Manager, and add the Network Policy and Access Services role. |
|
|
|
3. |
Close Server Manager. |
|
|
|
4. |
Open the Network Policy Server console. |
|
|
|
5. |
Register the server in AD DS. |
|
|
|
6. |
Leave the Network Policy Server window open. |
USE |
||
7. |
Open Routing and Remote Access. |
|||
|
|
|||
8. |
Disable the existing configuration. |
|
|
|
9. |
Reconfigure LON-RTR as a VPN Server using the following settings: |
|
|
|
|
o Local Area Connection 2 is the public interface. |
|
|
|
|
o The VPN server allocates addresses from the pool: 172.16.0.100 - 172.16.0.111. |
|
|
|
|
o The server is configured with the option No, use Routing and Remote Access to authenticate |
|||
|
connection requests. |
|
|
|
10. Start the VPN service. |
|
|
||
Configure a VPN Client |
PROHIBITED |
|||
1. |
Switch to LON-CL2, and sign in as Adatum\Administrator with the password of Pa$$w0rd. |
|||
2. |
Create a new VPN connection with the following properties: |
|||
|
|
|||
o Internet address to connect to: 10.10.0.1 o Destination name: Adatum VPN
o Allow other people to use this connection: true




