
Advanced Wireless Networks - 4G Technologies
.pdf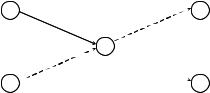
168 ADAPTIVE MEDIUM ACCESS CONTROL
Source 1 |
A |
E |
Sink 2 |
|
|
C |
|
Source 2 |
B |
D |
Sink 1 |
Figure 5.12 Two-hop network with two sources and two sinks.
every 5 s by each source node. In this experiment, the message inter-arrival period varies from 1 to 10 s.
For the highest rate with a 1 s inter-arrival time, the wireless channel is nearly fully utilized due to its low bandwidth. For each traffic pattern, 10 independent tests are done when using different MAC protocols. In each test, each source periodically generates 10 messages, which in turn is fragmented into 10 small data packets (40 bytes each). Thus, in each experiment, there are 200 data packets to be passed from their sources to their sinks. The energy consumption of the radio on each node to pass the fixed amount of data is measured . The actual time to finish the transmission is different for each MAC module. In the 802.11like MAC, the fragments of a message are sent in a burst, i.e. RTS and CTS are only used for the first fragment.
The 802.11-like MAC without fragmentation, which treats each fragment as an independent packet and uses RTS/CTS for each of them, is not measured, since it is obvious that this MAC consumes much more energy than the one with fragmentation. In S-MAC message passing is used, and fragments of a message are always transmitted in a burst. In the S-MAC module with periodic sleep, each node is configured to operate in the 50 % duty cycle.
Figure 5.13 shows the average energy consumption on the source nodes A and B. The traffic is heavy when the message inter-arrival time is less than 4 s. In this case, 802.11 MAC uses more than twice the energy used by S-MAC. Since idle listening rarely happens, energy savings from periodic sleeping is very limited. S-MAC achieves energy savings mainly by avoiding overhearing and efficiently transmitting long messages. When the message interarrival period is larger than 4 s, traffic load becomes light. In this case, the complete S-MAC protocol has the best energy performance, and far outperforms 802.11 MAC. Message passing with overhearing avoidance also performs better than 802.11 MAC. However, as shown in the figure, when idle listening dominates the total energy consumption, the periodic sleep plays a key role in energy savings.
Compared with 802.11, message passing with overhearing avoidance saves almost the same amount of energy under all traffic conditions. This result is due to overhearing avoidance among neighboring nodes A, B and C. The number of packets sent by each of them is the same in all traffic conditions.
5.4 MAC FOR AD HOC NETWORKS
A key component in the development of single channel ad hoc wireless networks is the MAC protocol with which nodes share a common radio channel. Of necessity, such a protocol

MAC FOR AD HOC NETWORKS |
169 |
Energy consumption (mJ)
1800 |
|
|
1600 |
|
|
1400 |
IEEE 802.11 – like protocol |
|
without sleep |
||
|
||
1200 |
|
|
1000 |
|
|
800 |
S-MAC without |
|
periodic sleep |
||
|
||
600 |
|
|
400 |
S-MAC with periodic sleep |
|
|
||
200 |
|
|
0 |
|
0 1 2 3 4 5 6 7 8 9 10 11
Message inter-arrival period (s)
Figure 5.13 Mean energy consumption on radios in each source node. (Reproduced by permission of IEEE [34].)
has to be distributed. It should provide an efficient use of the available bandwidth while satisfying the QoS requirements of both data and real-time applications. CSMA is one of the most pervasive MAC schemes in ad hoc wireless networks. CSMA is a simple distributed protocol whereby nodes regulate their packet transmission attempts based only on their local perception of the state, idle or busy, of the common radio channel.
Packet collisions are intrinsic to CSMA. They occur because each node has only a delayed perception of the other nodes’ activity. They also happen due to hidden nodes: two transmitting nodes outside the sensing range of each other may interfere at a common receiver. Many types of CSMA exist, but invariably the nodes that participate in a collision schedule the retransmission of their packets to a random time in the future, in the hope of avoiding another collision. This strategy, however, does not provide QoS guarantees for real-time traffic support.
MAC schemes for ad hoc wireless networks have been proposed, aimed either at improving the throughput over that of CSMA or at providing QoS guarantees for real-time traffic support. Among the first group of schemes is the multiple access collision avoidance protocol (MACA) [35], which forms the basis of several other schemes. With MACA, a source with a packet ready for transmission first sends a request-to-send (RTS) minipacket, which if successful elicits a clear-to-send (CTS) minipacket from the destination. Upon reception of the CTS minipacket, the source sends its data packet. In environments without hidden nodes, MACA may improve the throughput of the network over that attained with CSMA because collisions involve only short RTS minipackets rather than normal data packets as in CSMA. MACA also alleviates the hidden nodes problem because the CTS sent by the destination serves to inhibit the nodes in its neighborhood, i.e. exactly those nodes that may interfere with the ensuing packet transmission from source to destination. The floor acquisition multiple access (FAMA) class of protocols [36] includes several variants of MACA,
170 ADAPTIVE MEDIUM ACCESS CONTROL
one of which is immune to hidden nodes [37]. These protocols, however, have not been designed for QoS: control minipackets are subject to collisions, and their retransmissions are randomly scheduled.
The group allocation multiple access (GAMA) [38, 39] is an attempt to provide QoS guarantees to real-time traffic in a distributed wireless environment. In GAMA, there is a contention period where nodes use an RTS–CTS dialog to explicitly reserve bandwidth in the ensuing contention-free period. A packet transmitted in the contention-free period may maintain the reservation for the next cycle. The scheme is asynchronous and developed for wireless networks where all nodes can sense, and indeed receive, the communications from their peers. MACA/packet reservation (MACA/PR) [40] is a protocol similar to GAMA, but an acknowledgment follows every packet sent in contention-free periods to inform the nodes in the neighborhood of the receiver whether or not another packet is expected in the next contention-free cycle. These schemes deviate from pure carrier sensing methods in that every node has to construct channel-state information based on reservation requests carried in packets sent onto the channel.
In this section, we elaborate on the black-burst (BB) contention mechanism presented in Sobrinho and Krishnakumar [41]. With this mechanism, real-time nodes contend for access to the common radio channel with pulses of energy, BBs, the lengths of which are proportional to the time that the nodes have been waiting for the channel to become idle. The scheme is distributed and is based only on carrier sensing. It gives priority access to real-time traffic and ensures collision-free transmission of real-time packets. When operated in an ad hoc wireless LAN, it further guarantees bounded real-time delays. In addition, the BB contention scheme can be overlaid on current CSMA implementations, notably that of IEEE 802.11 standard for wireless LANs, with only minor modifications required to the real-time transceivers: the random retransmission scheme is turned off, and in substitution, the possibility of sending BBs is provided.
5.4.1 Carrier sense wireless networks
Carrier sense wireless networks are designed in such a way that the distance from which a node can sense the carrier from a given transmitter is different and typically larger than the distance from which receivers are willing to accept a packet from that same transmitter. In addition, the carrier from a transmitter can usually be sensed at a range beyond the range at which the transmitter may cause interference. To account for these differences, a wireless network is modeled as a set of nodes N , interconnected by links of three different types. Node i has a communication link with node j, if and only if in the course of time, it has packets to send to node j. Node i has an interfering link with node j if and only if any packet transmission with destination j that overlaps in time at j with a transmission from i is lost.
The lost packets are said to have collided with the transmission from i. Finally, node i has a sensing link with node j, if and only if a transmission by node i prevents node j from starting a new transmission, i.e. node i inhibits node j. The communication, interference and sensing graphs are denoted by GC = (N , LC), GI = (N , LI), and GS = (N , LS), respectively, where, LC, LI and LS are the edge sets (the links). The communication graph is a directed graph, whereas the interfering and sensing graphs are undirected. We assume that if node i has a communication link with node j, then i and j also have an interfering

|
MAC FOR AD HOC NETWORKS |
171 |
|
|
|
14 |
|
|
8 |
|
|
|
9 |
13 |
|
4 |
|
|
|
7 |
|
|
|
|
|
|
|
5 |
10 |
12 |
|
3 |
|
|
|
1 |
|
|
|
|
6 |
|
|
2 |
|
11 |
|
|
|
|
|
Communication |
Interfering |
Sensing |
|
Link |
Link |
Link |
|
Figure 5.14 A wireless network without hidden nodes. The shaded nodes form the set NS (9).
link between them. Similarly, an interfering link is also a sensing link, but not conversely. That is, LI LS: GI is a spanning subgraph of GS. Any node has an interfering and sensing link with itself, since whenever a node transmits, it cannot simultaneously receive or start another transmission. As an example in the wireless network of Figure 5.14, node 9 has a communication link with node 10, and thus these nodes have both an interfering and a sensing link between them. Nodes 10 and 13 have an interfering link, and thus they also have a sensing link between them. Finally, nodes 9 and 13 have only a sensing link between them. The links from a node to itself are not explicitly represented.
A path delay is associated with each sensing link to account for the propagation delay separating the nodes, the turn-around (round trip) time of the wireless transceivers, and the sensing delay. The path delay of link ij is denoted by τi j . Since the sensing graph is undirected, τi j = τ ji . The path delays further satisfy the two conditions τi j > 0 and
τik + τk j > τi j , for ik, k j, i j LS.
Let τ @ max(τi j ). The sets NI(i) and NS(i) represent the nodes that are neighbors of i, i included, in the interfering and sensing graphs, respectively. In Figure 5.14, NI(10) = {9, 10, 11, 12, 13} and NS(9) = {7, 8, 9, 10, 11, 12, 13}. For communication link ij, the set of nodes which are interfering neighbors of j but are not sensing neighbors of i, i.e. the set, NI( j) ∩ [N − NS(i)], is the set of nodes hidden from ij. A node in this set will not sense an ongoing packet transmission from i to j and may initiate its own packet transmission that will collide at j. In a wireless network without hidden nodes, we have NI( j) NS(i) for every i j LC. The network of Figure 5.14 does not have hidden nodes. Nevertheless, the common radio channel can be reused in space. For example, a packet transmission from node 9 to node 8 can coexist in time without collisions with a packet transmission from node 5 to node 7. We use the term ‘wireless LAN’ for wireless networks in which GI = GS forms a complete graph. In a wireless LAN, all nodes can sense each other’s transmissions. The CSMA/CA protocol of the IEEE 802.11 standard defines three interframe spacings, tshort, tmed, tmed ≥ 2τ + tshort and tlong, tlong ≥ 2τ + tmed. If a node with a packet that is ready for transmission has perceived that the channel is idle during a long interframe spacing of length tlong, the node immediately starts the transmission of the packet. Otherwise, it waits until that condition is satisfied and enters into backoff.
172 ADAPTIVE MEDIUM ACCESS CONTROL
Likewise, a node whose packet has experienced c consecutive collisions enters into backoff. In this mode, the node chooses a random number of slots s uniformly distributed between zero and min {32 × 2c − 1,255} and sets a timer with an initial value s × tslot units of time, where tslot, tslot ≥ 2τ , is the length of a slot. The timer counts down only while the channel has been perceived idle for more than tlong units of time – it is frozen during a medium busy condition – and the packet is (re)transmitted as soon as the timer reaches zero. A node learns of the success or failure of its transmission through a positive acknowledgment scheme; the recipient of a correctly received packet sends back an acknowledgment minipacket within an interval of time of length tshort.
BB contention is a MAC mechanism developed to provide QoS guarantees to real-time traffic over carrier sense wireless networks. The real-time applications considered are those like voice and video that require more or less periodic access to the common radio channel during long periods of time denominated sessions. The main performance requirement for these applications is bounded end-to-end delay, which implies a bounded packet delay at the MAC layer. This is the goal of BB contention. Real-time nodes contend for access to the channel after a medium interframe spacing of length tmed, rather than after the long interframe spacing of length tlong used by data nodes. Thus, real-time nodes as a group have priority over data nodes.
Instead of sending their packets when the channel becomes idle for tmed, real-time nodes first sort their access rights by jamming the channel with pulses of energy, denominated BBs. The length of a BB transmitted by a real-time node is an increasing function of the contention delay experienced by the node, measured from the instant when an attempt to access the channel has been scheduled until the channel becomes idle for tmed, i.e. until the node starts the transmission of its BB. To account for the path delays in the network, BBs are formed by an integral number of black slots, each of length tbslot, with tbslot not smaller than the maximum round-trip path delay 2τ . Now, we would like the BBs sent by distinct real-time nodes when the channel becomes idle for tmed to differ by at least one black slot. To this end, we assume that every real-time packet transmission lasts at least a certain time tpkt and that real-time nodes only schedule their next transmission attempts – to a time tsch in the future – when they start a packet transmission. If a node starts a packet transmission at time u and that transmission is successful, that means that no other real-time node started a packet transmission during an interval of length 2tpkt around time u. Therefore, the next scheduled attempt made by the node in question is also staggered in time by tpkt from the scheduled access attempts made by the other nodes. Counting the number of black slots to be sent in a BB in units of tpkt, we obtain the desired property that distinct nodes contend with BBs comprising different numbers of black slots. Following each BB transmission, a node senses the channel for an observation interval of length tobs to determine without ambiguity whether its BB was the longest of the contending BBs. The winning node will transmit its real-time packet successfully and schedule the next transmission attempt. On the other hand, the nodes that lost the BB contention wait for the channel to once again become idle for tmed, at which time they send new longer BBs. In conclusion, once the first real-time packet of a session is successfully transmitted, the mechanism ensures that succeeding real-time packets are also transmitted without collisions. In the end, real-time nodes appear to access a dynamic time division multiplexing (TDM) transmission structure without explicit slot assignments or slot synchronization. In the sequel a detailed description of the access rules followed by every real-time node is presented. Every real-time packet lasts for at least a certain amount of time tpkt tpkt ≥ 2τ , when transmitted on the channel. At the
MAC FOR AD HOC NETWORKS |
173 |
beginning of a session, a real-time node uses conventional CSMA/CA rules, possibly with a more expedited retransmission algorithm, to convey its first packet until it is successful. Subsequent packets are transmitted according to the mechanisms, described below, until the session is dropped.
Whenever a real-time node transmits a packet, it further schedules its next transmission attempt to a time tsch in the future, where tsch is the same for all nodes. Suppose, then, that a real-time node has scheduled an access attempt for the present time. If the channel has been idle during the past medium interframe interval of length tmed, the node starts the transmission of a BB. Otherwise, it waits until the channel becomes idle for tmed and only then starts the transmission of its BB. The length b of the BB sent by the node is a direct function of the contention delay it incurred, dcont:
b(dcont) = 1 + |
dcont |
tbslot |
tunit |
where tbslot is the length of a black slot, the parameter tunit is the unit of time used to convert contention delays into an integral number of black slots, and x is the floor of x, i.e. the largest integer not larger than x. Correct operation of the scheme requires that tunit ≤ tpkt. After exhausting its BB transmission, the node waits for an observation interval tobs, the length of which has to satisfy tobs ≤ tbslot and tobs ≤ tmed, to see if any other node transmitted a longer BB, implying that it would have been waiting longer for access to the channel. If the channel is perceived idle after tobs, then the node (successfully) transmits its packet. On the other hand, if the channel is busy during the observation interval, the node waits again for the channel to be idle for tmed and repeats the algorithm.
The start of packet transmissions from different nodes is shifted in time by at least tpkt. Since it is only when a node initiates the transmission of a packet that it schedules its next transmission attempt to a time tsch in the future, the contention delays of different nodes will likewise differ by at least tpkt. Therefore, taking tunit ≤ tpkt, the BBs of different nodes differ by at least one black slot, and thus every BB contention period produces a unique winner. That winner is the node that has been waiting the longest for access to the channel. The observation interval tobs cannot last longer than the black slot time, i.e. tobs ≤ tbslot, so that a node always recognizes when its BB is shorter than that of another contending node. It also has to be shorter than the medium interframe spacing, i.e. tobs ≤ tmed, to prevent realtime nodes from sending BBs by the time that a real-time packet transmission is expected. Overall, the BB contention scheme gives priority to real-time traffic, enforces a round-robin discipline among real-time nodes, and results in bounded access delays to real-time packets.
BB contention can also be used to support real-time sessions with different bandwidth requirements, which might be useful for multimedia traffic. On the one hand, distinct realtime sessions may have the corresponding nodes send packets of different sizes when they acquire access rights to the channel. On the other hand, the BB mechanism can be enhanced to accommodate real-time sessions with different scheduling intervals as long as the set of values allowed for the scheduling interval tsch is finite and small. In the latter case, BB contention proceeds in two phases. Real-time nodes first sort their access rights based on contention delays as before. However, it is now possible for two nodes with different scheduling intervals to compute BBs with the same number of black slots. Hence, after this first phase, a real-time node contends again with a new BB, the length of which univocally identifies the scheduling interval being used by the node.
174 ADAPTIVE MEDIUM ACCESS CONTROL
5.4.2 Interaction with upper layers
5.4.2.1 Operation with feedback
If a real-time node were alone in the network, two consecutive real-time packet transmissions belonging to the same session would be separated in time by exactly tacc, tacc @ tsch + tbslot + tobs. The access delays measure the deviation from this ideal situation. Specifically, an access delay is the time that elapses from the moment an access attempt occurs until the node is able to transmit the corresponding real-time packet, corrected for tbslot + tobs. For n ≥ 2, the nth access delay associated with a session is denoted by d(n) and is given by d(n) = (u(n) − u(n−1) − tacc), where u(n) is the instant of time when the node started the transmission of its nth packet. Given the maximum length of data packets, the rate of realtime sessions and number of real-time nodes, the BB mechanism guarantees that the access delays are bounded and usually by a very small value dmax.
When a node is the source node of a session, the contents of its real-time packets can reflect the access delays incurred in contending for access to the channel. Typically, a realtime application generates blocks of information bits at regular intervals of time, of length much smaller than tacc. The block delay is the time interval that elapses from the moment an information block is made available by the application until it is successfully transmitted at the MAC layer (corrected for tbslot + tobs and neglecting processing delays). The relation between access and block delays depends on how the application blocks of information are packetized for transmission at the MAC layer. One possibility is to have the MAC layer convey in a packet all the information blocks generated up to the instant when the node is about to start a packet transmission. The length of a real-time packet would thus grow with the access delay incurred by the node. The block delay of the oldest block conveyed in the packet would consist of tacc, plus the corresponding access delay: the block delay would never exceed tacc + dmax. In general, however, it is not feasible to assemble a packet at the time that its transmission should start, and further, the MAC layer usually contains a single buffer that we must ensure is filled with a packet by the time access to the channel is granted.
For a realistic alternative within the spirit of this section, consider a simplified communication architecture in which a real-time application puts its generated blocks of information into an application buffer. Whenever the node successfully transmits a packet it signals the application, which will assemble the next packet with all the blocks of information currently queued at the application buffer, plus the blocks that will be generated during the next interaccess interval of length tacc. At this later time, the packet is delivered to the MAC layer for transmission. With this procedure, the MAC layer always has a packet ready for transmission by the time it acquires undisputed access to the channel. When a node transmits its nth packet at time u(n), it leaves in the application buffer the blocks of information generated during the previous d(n) units of time; they will be part of the contents of the (n + 1)th packet. The latter packet further incurs an access delay of d(n+1) at the MAC layer. Therefore, the block delay of the oldest block conveyed in the (n + 1)th packet is not greater than (dn + tacc + dn+1): the block delay during a session never exceeds (tacc + 2dmax).
5.4.2.2 Operation without feedback
In the previous section, the contents of a real-time packet depended on the access delays incurred by a node. There is a direct coupling between the MAC layer and the real-time application. A simpler communication architecture may be desired in which already assembled
REFERENCES |
175 |
packets are passed onto the MAC layer for transmission one by one. This is also the situation encountered when a node is simply relaying real-time packets arriving from a distant source.
Suppose that real-time packets are presented to the MAC layer periodically, one every trdy units of time. The packet delay is the time that elapses from the moment a packet is available for transmission until it is successfully transmitted at the MAC layer (corrected for tbslot + tobs). The packet delay of the nth packet ω(n) is given by ω(n) = (u(n) − t(n) − tbslot − tobs), where t(n) is the instant of time when the nth packet becomes ready for transmission,
t(n) = t(1) + (n − 1)trdy .
Clearly, we should not choose tsch + tbslot + tobs = trdy. If that choice was made, the instants when the node accesses the channel would start drifting in relation to the arrival times of new packets, and the node would not keep up with the packet arrival rate. Indeed, the packet delay of the nth packet would be
n
ω(n) = ω(1) + d(i) i=2
which would grow monotonically with the number of packets already transmitted. Consider instead a preventive approach whereby a real-time node schedules its next
transmission attempt short of the inter-arrival time for packets trdy. Specifically, when a real-time node transmits a packet, it schedules the next transmission attempt to time tsch in the future, now with tsch = trdy − tbslot − tobs − δ, where δ, δ > 0, is called the slack time. At a scheduled access attempt, a real-time node will only start contending for access to the channel if a real-time packet is available for transmission. Otherwise, it waits for a ready packet and only then starts to contend for access to the channel. The correctness of the BB contention mechanism is preserved as long as the contention delays used to compute the lengths of BBs are always counted from the scheduled access attempts up to the time when the channel becomes idle for tmed.
REFERENCES
[1]IEEE Std 802.11–1999, Part 11: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications, Reference number ISO/IEC 8802-11:1999 (E), IEEE Std 802.11, 1999.
[2]IEEE 802.11 Wireless Local Area Networks; http://grouper.ieee.org/groups/802/11/.
[3]IEEE 802.11e/D4.0, Draft Supplement to Part 11: Wireless Medium Access Control (MAC) and Physical Layer (PHY) Specifications: Medium Access Control (MAC) Enhancements for Quality of Service (QoS), November 2002.
[4]S. Choi, J. Prado, S. Shankar and S. Mangold, IEEE 802.11e Contention-Based Channel Access (EDCF) Performance Evaluation, in Proc. IEEE ICC 2003, Anchorage, AK, May 2003.
[5]P. Garg, R. Doshi, R. Greene, M. Baker, M. Malek and X. Cheng, Using IEEE 802.11e MAC for QoS over wireless, in Proc. IEEE Int. Performance Computing and Communications Conf., Phoenix, AZ, April 2003.
[6]A. Banchs, X. Perez-Costa, and D. Qiao, Providing throughput guarantees in IEEE 802.11e wireless LANs, in Proc. 18th Int. Teletraffic Congr. (ITC-18), Berlin, September 2003.
176ADAPTIVE MEDIUM ACCESS CONTROL
[7]Y. Xiao, Enhanced DCF of IEEE 802.11e to Support QoS, in Proc. IEEE WCNC 2003, New Orleans, LA, March 2003.
[8]S. Mangold, G. Hiertz and B. Walke, IEEE 802.11e wireless LAN – resource sharing with contention based medium access, in IEEE PIMRC 2003, Beijing, September 2003.
[9]G. Bianchi, Performance analysis of the IEEE 802.11 distributed coordination function, IEEE JSAC, vol. 18, no. 3, 2000, pp. 535–547.
[10]IEEE Std 802.11b-1999, Supplement to Part 11: Wireless Medium Access Control (MAC) and Physical Layer (PHY) Specifications: Higher-Speed Physical Layer Extension in the 2.4 GHz Band, September 1999.
[11]Z. Hadzi-Velkov and B. Spasenovski, Saturation throughput-delay analysis of IEEE 802.11 DCF in fading channel, in Proc. IEEE ICC 2003, Anchorage, AK, May 2003.
[12]S. Mangold, S. Choi, G. Hiertz, O. Klein and B. Walke, Analysis of IEEE 802.11e for QoS support in wireless LANs, IEEE Wireless Commun., vol. 10, no. 6, 2003, pp. 40–50.
[13]IST WSI, The Book of Visions 2000: Visions of the Wireless World, Version 1.0, 2000.
[14]Z. Tao and S. Panwar, An analytical model for the IEEE 802.11e enhanced distributed coordination function, IEEE Int. Conf. Communications, vol. 7, 20–24 June 2004, pp. 4111–4117.
[15]H. Singh and S. Singh, Doa-aloha: slotted aloha for ad hoc networking using smart antennas, in IEEE VTC Fall’03, 6–9 October 2003.
[16]H. Singh and S. Singh, A MAC protocol based on adaptive beamforming for ad hoc networks, in IEEE Pimrc’03, 7–10 September 2003.
[17]R.R. Choudhury, X. Yang, R. Ramanathan and N.H. Vaidya, Using directional antennas for medium access control in ad hoc networks, in ACM/SIGMOBILE MobiCom 2002, 23–28 September 2002.
[18]L. Bao and J.J. Garcia-Luna-Aceves, Transmission scheduling in ad hoc networks with directional antennas, in ACM/SIGMOBILE MobiCom 2002, 23–28 September 2002.
[19]S. Bellofiore, J. Foutz, R. Govindarajula, I. Bahceci, C.A. Balanis, A.S. Spanias, J.M. Capone and T.M. Duman, Smart antenna system analysis, integration, and performance for mobile ad-hoc networks (manets), IEEE Trans. Antennas and Propagation, vol. 50, no. 5, 2002, pp. 571–581.
[20]T. ElBatt and B. Ryu, On the channel reservation schemes for ad hoc networks utilizing directional antennas, in WPMC’02, 2002.
[21]N. Fahmy, T.D. Todd and V. Kezys, Ad hoc networks with smart antennas using 802.11-based protocols, in IEEE ICC’02, 2002.
[22]G.M. Sanchez, Multiple access protocols with smart antennas n multihop ad hoc ruralarea networks, M.S. thesis, Royal Institute of Technology, Sweeden, Radio Communication Systems Laboratory, Department of Signals, Sensors and Sytems, June 2002.
[23]R. Bagrodia, M. Takai, J. Martin and A. Ren, Directional virtual carrier sensing for directional antennas in mobile ad hoc networks, in ACM/SIGMOBILE MobiHoc 2002, October 2002.
[24]T. Nandagopal, T.-E. Kim, X. Gao and V. Bharghavan, Achieving MAC layer fairness in wireless packet networks, in ACM MOBICOM’00, August 2000, pp. 87–98.
[25]B. Bensaou, Y. Wang and C.C. Ko, Fair medium access in 802.11 based wireless ad-hoc networks, in ACM MOBIHOC’00, August 2000, pp. 99–106.
REFERENCES 177
[26]V. Bharghavan, A. Demers, S. Shenker and L. Zhang, Macaw: a media access protocol for wireless lans, in ACM SIGCOMM’94, August 1994, pp. 212–225.
[27]H. Singh and S. Singh, Smart-802.11b MAC protocol for use with smart antennas, in IEEE Int. Conf. Communications, vol. 6, 20–24 June 2004, pp. 3684–3688.
[28]A. Woo and D. Culler, A transmission control scheme for media access in sensor networks, in Proc. ACM/IEEE Int. Conf. Mobile Computing and Networking, Rome, July 2001, pp. 221–235.
[29]F. Bennett, D. Clarke, J.B. Evans, A. Hopper, A. Jones and D. Leask, Piconet: embedded mobile networking, IEEE Person Commun. Mag., vol. 4, 1997, pp. 8–15.
[30]S. Xu and T. Saadawi, Does the IEEE 802.11 MAC protocol work well in multihop wireless ad hoc networks?, IEEE Commun. Mag., vol. 36, 2001, pp. 130–137.
[31]Y.-C. Tseng, C.-S. Hsu and T.-Y. Hsieh, Power-saving protocols for IEEE 802.11based multi-hop ad hoc networks, in Proc. IEEE INFOCOM, New York, June 2002, pp. 200–209.
[32]V. Bharghavan, A. Demers, S. Shenker and L. Zhang, MACAW: a media access protocol for wireless lans, in Proc. ACM SIGCOMM, London, Septembar 1994, pp. 212– 225.
[33]Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specification, IEEE Std 802.11, 1999.
[34]W. Ye, J. Heidemann and D. Estrin, Medium access control with coordinated adaptive sleeping for wireless sensor networks, IEEE/ACM Trans. Networking, vol. 12, no. 3, June 2004, pp. 493–506.
[35]P. Karn, MACA – A new channel access method for packet radio, in Proc. ARRL/CRRL Amateur Radio Ninth Computer Networking Conf., ARRL, 1990, pp. 134–140.
[36]C. Fullmer and J. Garcia-Luna-Aceves, Floor acquisition multiple access (FAMA) for packet-radio networks, in Proc. SIGCOMM’95, Cambridge, MA, 1995, pp. 262–273.
[37]C. Fullmer and J. Garcia-Luna-Aceves, Solutions to hidden terminal problems in wireless networks, in Proc. SIGCOMM’97, vol. 2, Cannes, 1997, pp. 39–49.
[38]A. Muir and J. Garcia-Luna-Aceves, Supporting real-time multimedia traffic in a wireless LAN, in Proc. SPIE Multimedia Computing and Networking 1997, San Jose, CA, 1997, pp. 41–54.
[39]R. Garces and J. Garcia-Luna-Aceves, Collision avoidance and resolution multiple access with transmission groups, in Proc. IEEE INFOCOM’97, Kobe, 1997, pp. 134– 142.
[40]C. Lin and M. Gerla, Asynchronous multimedia multihop wireless networks, in Proc. IEEE INFOCOM’97, Kobe, 1997, pp. 118–125.
[41]J.L. Sobrinho and A.S. Krishnakumar, Real-time traffic over the IEEE 802.11 medium access control layer, Bell Labs Tech. J., vol. 1, 1996, pp. 172–187.
