- •Государственное образовательное учреждение
- •Courts and trials (topical vocabulary)
- •Set Work
- •I. Study the above given lexical units.
- •II. Give words for the following definitions.
- •III. Translate into English:
- •Crime and punishment
- •Set Work
- •Set Work
- •Set Work
- •I. What would you have done?
- •II. Look at these statements. What do you think about them?
- •III. Look at this list of ‘crimes’. Try and rate each crime on a scale from 1-10. (1 is a minor misdemeanor, 10 is a very serious crime.) They are in no order.
- •IV. Compare your list with another student’s. Which of you would be the harsher judge? Which would be the kinder?
- •Thief challenges dose of shame as punishment
- •Set Work
- •Women behind bars
- •Set Work
- •VI. State the idea behind the lines below and enlarge on it.
- •VII. Sum up the key points of the article.
- •VIII. Points for discussion.
- •Justice in los angeles
- •Set Work
- •V. Points for discussion.
- •VI. Sum up the article and single out its main points. Черное плюс белое равняется красному?
- •Set Work
- •I. Think of the best English equivalents of:
- •II. Say what you know about:
- •III. Points for discussion.
- •IV. Comment on the choice of the headline.
- •Set Work
- •VIII. Enlarge on the idea.
- •IX. Points for discussion.
- •X. Role play.
- •Set Work
- •Set Work
- •VI. Give the gist of the article.
- •VII. Points for discussion.
- •Век бы свободы не видать!
- •Set Work
- •Set Work
- •I. Say what is meant by the following words and word combinations. Reproduce the situations in which they were used.
- •II. Find in the article the English for:
- •III. Interpret the lines below.
- •IV. Comment on the author’s choice of the headline and formulate the key idea running through the article.
- •V. Points for discussion.
- •How british burglars pick their victims
- •Set Work
- •I. Master the pronunciation of the words below. Learn and translate them.
- •II. Explain what is meant by:
- •III. Look through the article for the following English equivalents of:
- •IV. State the difference between the words below. Give examples to illustrate their usage.
- •V. Translate the following sentences.
- •VI. Pete (the burglar described in the article) says he is ten stone. How many kilos is it? How many stones do you weigh?
- •VII. Interpret the idea expressed in the lines below.
- •VIII. Points for discussion.
- •A life inside
- •I. Define the following words and word combinations. Reproduce the situations in which they occur.
- •II. Scan the article for the English equivalents of:
- •III. State the difference between the words below. Give examples to illustrate their usage.
- •IV. Explain what is meant by:
- •V. Say whether you agree or disagree with the lines below.
- •Set Work
- •I. Explain the meaning of the words below. Say how they were used in the article.
- •II. Give the English equivalents of the following word combinations:
- •III. Comment on the statements below.
- •IV. Translate the following sentences.
- •V. Points for discussion.
- •VI. Speak about your stand on capital punishment as “the only way to deter criminals”. To back up either of your viewpoints use the key statements.
- •«Палач является в застенок со всеми инструментами» так добивались правды
- •Set Work
- •III. Practise the pronunciation of the words below:
- •IV. Explain what is meant by:
- •V. State the difference between the following words, give examples to illustrate their usage.
- •VI. What other arguments for and against capital punishment can you add to the list?
- •40 Тезисов в осуждение убийцы
- •Set Work
- •Set Work
- •I. Choose the correct meaning according to the passage.
- •II. Give the Russian equivalents of the following vocabulary units:
- •III. Say if the problem of capital punishment has always been vital. Back up your opinion. Как, где и за что казнят
- •Set Work
- •Set Work
- •Set Work
- •Set Work
- •Set Work
- •II. Find in the article the Russian for:
- •III. Say if you share the idea expressed in the sentences below:
- •IV. Explain the difference between:
- •V. Points for discussion.
- •VI. Render the article into English, trying to use as many words under study as you can.
- •VII. Comment on the headline and formulate the author’s message.
- •Inside the new alcatraz
- •Set Work
- •IX. Points for discussion.
- •X. Comment on the headline.
- •XI. Describe a prison for hard-core criminals, as you see it. Смертникам жизнь хуже расстрела
- •Set Work
- •Set Work
- •I. Think of the best English equivalents of:
- •II. Say what you know about:
- •State power and crime
- •Set Work
- •I. Say what is meant by the words and word combinations below:
- •II. Find in the article the English for:
- •III. Say how you understand the lines below and enlarge on the idea.
- •IV. Is it possible to oppose the demoralization of the very fundaments of the life of the nation? What is the general path of the sanitation of public life and the state itself?
- •V. Sum up the main points of the article. Какие законы нам не указ Почему россияне не верят в законы
- •Set Work
- •I. Think of the best English equivalents of:
- •II. What’s the English for?
- •The holocaust in the dock
- •Set Work
- •VII. Give the gist of the article.
- •VIII. Describe the Swiss-Nazi case and formulate the author’s vision of the problem.
- •IX. How is the Swiss-Nazi case likely to end? What’s the rub? Will justice be done at long last? the making of a suicide bomber
- •Set Work
- •I. Master the pronunciation of the words below. Learn and translate them.
- •II. Explain the meaning of the words below. Say how they were used in the article.
- •III. Look through the article for the English equivalents of:
- •IV. Say what you know about:
- •V. Write out expressions with the word “suicide” and explain what they mean.
- •VI. Say whether you agree or disagree with the following statements and enlarge on them.
- •VII. Points for discussion.
- •VIII. Do a library research on some terrorist organisation and make a short report in class. Terrorist infiltrations
- •Set Work
- •VI. Comment on the author’s choice of the headline and formulate the message.
- •VII. Points for discussion.
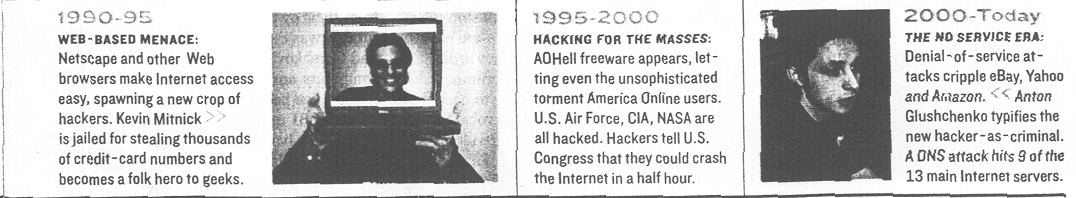
- •VIII. Say if you’ve read any of the books mentioned in the article. Do such kinds of books appeal to you? hacking for dollars
- •Set Work
- •I. Learn and practise the pronunciation of the words below. Translate them into Russian.
- •II. Define the computer-related word combinations used in the article. Reproduce the context in which they were used.
- •III. Find in the article the English for:
- •IV. Say what is meant by the words and word combinations below. How were they used in the article?
- •V. State the difference between the words below. Give examples to illustrate their usage.
- •VI. Clarify the idea behind the following lines.
- •VII. Outline the main points of the article and dwell upon each of them.
- •VIII. Points for discussion.
- •IX. Make up a dialogue between two cybercops. Use the words from the article.
- •Set Work
- •I. Learn the pronunciation of the words below. Translate them into Russian.
- •II. Define the words and word combinations below. Say how they were used in the article.
- •III. Scan the article for the English equivalents of:
- •IV. Look through the article for the word combinations with the word “online.” Write them out and explain what they mean.
- •V. Explain what is meant by:
- •VI. Fill in the correct preposition. Check against the text.
- •VII. Say how you understand the following lines.
- •VIII. Points for discussion.
- •Internet как инструмент совершения киберпреступлений
- •Set Work
- •I. Render the above given article into English.
- •II. Points for discussion.
- •Spyware hits business
- •Set Work
- •I. Master the pronunciation of the words below. Learn and translate them.
- •II. Explain what is meant by:
- •III. Look through the article for the English equivalents of:
- •IV. What do the following abbreviations stand for:
- •V. State the difference between the words below. Give examples to illustrate their usage.
- •VI. Add some more words to the given string.
- •VII. Fill in the correct prepositions. Check against the text.
- •VIII. Interpret the lines below.
- •IX. Points for discussion.
- •Mobile phone crime blitz launched
- •Set Work
- •Set Work
- •VI. Sum up the key points of the article.
- •VII. Points for discussion.
- •The gentleman thief
- •Set Work
- •Drugs and crime
- •Set Work
- •I. Transcribe and learn the following words:
- •II. Find out and say what is meant by:
- •III. Say what you know about the units of weight mentioned in the article. In what connections were they used?
- •IV. Reveal the difference between:
- •V. Say how you understand:
- •VI. Learn the pronunciation of the following deadly drugs.
- •VII. Give English equivalents for:
- •VIII. Answer the following questions.
- •IX. Translate the following sentences into English.
- •Наркотикам – бой…и герл
- •Set Work
- •Set Work
- •I. Define the words and word combinations below. Reproduce situations in which they occur in the article.
- •II. Look through the article for the following English equivalents:
- •III. Specify the meaning of the prefix over-. Write out the examples with this prefix from the article and explain their meaning. Think of some other examples and dwell upon them.
- •IV. Say how you understand the given lines.
- •V. Points for discussion.
- •Тяга к наркотикам ничуть не ослабла
- •Set Work
- •Set Work
- •I. Say what is meant by the following vocabulary units and in what connection they are used in the article.
- •Вам марихуаны? пожалуйста!
- •Set Work
- •Set Work
- •V. What addictive substances are mentioned in the article? In what ways are they consumed by addicts?
- •VI. Explain how you understand the following phrases:
- •VII. State the difference between the words below. Give examples to illustrate their usage.
- •VIII. Interpret the idea expressed in the given lines.
- •IX. Give the gist of the article and formulate its key idea.
- •X. Comment on the headline.
- •XI. Points for discussion.
- •A shot of sanity
- •Set Work
- •VIII. Give the gist of the article and say what you think of the idea put forward by the author.
- •IX. Points for discussion.
- •Cocaine cartel smashed
- •Set Work
- •I. Think of the best English variant to say:
- •Set Work
- •Set Work
- •I. Supply the English equivalents for the following words and word combinations:
- •Set Work
- •Set Work
- •I. What answers to the above questions does the article offer?
- •II. Scan the article for the English equivalents of the Russian words below and learn them.
- •III. Explain what is meant by:
- •IV. Make up a dialogue (based on the words from task II) between two criminologists.
- •V. Points for discussion.
- •I. Render the below article into English.
- •II. Say whether you share the author’s thesis. How it all starts inside your brain
- •Set Work
- •I. Master the pronunciation of the words below. Learn and translate them.
- •II. Define the following words and word combinations below. Reproduce the situations in which they occur.
- •III. Scan the article for the English equivalents of:
- •IV. Explain what the following abbreviations stand for.
- •V. State the difference between the words below. Give examples to illustrate their usage.
- •VI. Explain how you understand:
- •VII. Say what you know about:
- •VIII. Find in the article the evidence to support the following statements.
- •IX. Points for discussion.
- •Агрессивное поведение запрограммировано еще при рождении преступник разрушает сам себя
- •Set Work
- •VI. Sum up the main points of the article and say if you share the journalist’s stand.
- •VII. Points for discussion.
- •1. Is society or are people to blame for different misdemeanors and felonies? 2. How can people be made less aggressive? of criminals and ceos
- •Set Work
- •V. Interpret the lines below.
- •VI. Say what you know about:
- •VII. Sum up the key points of the article and formulate the author’s thesis.
- •VIII. Comment on the choice of the headline.
- •IX. Points for discussion.
- •Set Work
- •VI. Do you agree that:
- •VII. Sum up the key points of the article.
- •VIII. Points for discussion.
- •Death penalty
- •Убийство должно караться смертью!
- •Cops and robbers (and drug pushers and murderers…)
- •I. Read the following article to find out:
- •Computer hacking – high-tech crime
- •II. Find words or phrases in the text which mean the same as:
- •III. Now complete these statements by choosing the answer which you think fits best.
- •Vocabulary Tests
- •I. Crime. Put each of the following words and phrases into its correct place in the passage below.
- •II. Law breakers. Give the name of the defined law breaker.
- •III. Law breakers. Match the criminal with the definition.
- •IV. Law breakers. Choose the right answer.
- •V. Law breakers. Choose the correct answer.
- •VI. Law breakers. By moving vertically or horizontally (forwards or backwards) find twelve kinds of criminal.
- •VII. Police. Choose the right answer.
- •VIII. Trial. If you commit a crime you may be:
- •IX. Trial. Choose the right answer.
- •X. Trial. Choose the right answer.
- •XI. Punishment. Match each punishment with its description.
- •XII. Punishment. Choose the right answer.
- •XIII. Punishment. Put each of the following words and phrases into its correct place in the passage below.
- •Trial by Jury
- •XIV. Crime and punishment. Choose the right answer.
- •XV. Crime and punishment. Choose the word or phrase that best keeps the meaning of the original sentence if it is substituted for the capitalized word.
- •Vocabulary Test
- •Фантастический процесc
- •Set Work
- •Твое имя в грязи
- •Methods and measures
- •Третье место за воровство
- •Is a crime crackdown a challenge of the time?
- •Государственное образовательное учреждение высшего профессионального образования «Липецкий государственный педагогический университет»
- •398020 Г. Липецк, ул. Ленина, 42
Set Work
I. Define the words and word combinations below. Say how they were used in the article.
Inscrutable, to patch up survivors, page-turner, to atone, lame-brained, to rip, sardonic, to make sth the point of sth, imam, guidance counselor, infiltration, blanch.
II. Scan the article for the English equivalents of:
злоумышленник, затмевать, удовлетворенный, бегающие глаза, безразличные голоса, слова песни, формировать чье-л. сознание, по-любительски, по сути, школьник, искупление.
III. Specify the difference between:
consciousness – conscience;
to influence – to affect;
search – quest;
counsel – counselor.
IV. Say what you know about:
a) anarchists, the Qur’an, hedonism, nihilism;
b) Don DeLillo, Swede Levov, Philip Roth, Jennifer Egan, Yasmina Khadra, John Updike;
c) New Jersey, Manhattan.
V. Explain what is meant by the lines below.
Although topical fiction is often thin and amateurishly reported, novelists still insist on writing books “ripped from today’s headlines.”
We rarely get inside their heads and, when we do, the view just isn’t worth the trip.
“Aziz had been seduced by his rage years ago,” Jennifer Egan writes of the terrorist in her 2001 “Look at Me,” “caught in its swooning thrall until everything else in the world seemed faint beside it.”
Khadra isn’t in the redemption business: his true subject isn’t terrorism, but blindness and ambiguity, which have been around before there were headlines to rip them out of.
“…They lack true faith; they are not on the Straight Path; they are unclean.”
It’s his guidance counselor who puts terrorism in context.
If terrorists only wanted to overthrow writing like this, fine.
VI. Comment on the author’s choice of the headline and formulate the message.
VII. Points for discussion.
Are terrorist attacks more shocking in real world or in the literary world?
Why does the journalist refer to the terrorist as to the arch-enemy of all civilization? What is his point?
Do you agree that the suicide bomber is the least understandable variety of terrorist?
Why does the journalist choose the word “monomaniac” to describe a suicide bomber?
What is the journalist’s point of retelling plots of different modern books zeroing on terrorism?
Why does the journalist call the terrorist “the writer’s evil twin”?
Is the terrorist an ideal literary character?
VIII. Say if you’ve read any of the books mentioned in the article. Do such kinds of books appeal to you? hacking for dollars
The lone computer geek – a bit rebellious, but with a heart of gold – is being eclipsed by the hardened professional criminal, who uses the internet for spying, stealing and extortion.
In the high-tech battlefield of cyberspace, the thirtysomething Russian with the jet black goatee and the new denim coat considers himself a freedom fighter – a descendant of those legendary computer geeks whose cyberstunts drove the establishment wild and helped define a unique Internet culture. Like his hacker predecessors, he has his own subversive code, this one tinged with the slogans of anti globalization. He talks of “freedom,” “the unhindered flow of ideas” and the need to break the stranglehold of “monster corporations like Microsoft.” (He won’t hack into Russian companies.) “I live in the shadows. That is where I want to be,” says the hacker – we’ll call him Dmitry – over a late-night meal in a Moscow restaurant. “I don’t need to prove anything to anyone.”
Dig a little deeper and you’ll find there’s something that differentiates this New Age cybersurfer from his high-minded brethren. Last year Dmitry netted $300,000 – stolen from major American corporations. Like a slick businessman, Dmitry arrives for his secret rendezvous with Newsweek accompanied by his lawyer. He works as part of a hacker team, composed of 10 or so experienced criminals, each with his own specialty. His job: to break into networks, opening the way for his confederates to steal and decode company information. He’ll work 16-hour days for six months preparing for an assault on a Western corporation that might last just minutes. “It’s like a military attack,” he says. “At first you do intelligence. You watch their behavior. You get ready for X-hour. When you’re 90 percent sure of success, you attack.”
The days when the lone hacker was the symbol of all that was good about the Internet seem to be fading fast. Dmitry is part of perhaps the fastest growing criminal enterprise of the 21st century. These hardened pros are well schooled in the arts of extortion, fraud and intellectual-property theft. Sure, many retain some of the rebellious affectations of their predecessors by wrapping themselves in anti-establishment, anti-globo speak. But they are increasingly organized, sophisticated and often ruthless. And they are costing companies and individuals billions of dollars. A growing number of them live far beyond the clutches of U.S., Japanese and European law-enforcement officials, in places like Russia, Brazil, China and South Korea. From distant domains they route their signals through multiple countries to throw the digital cops off their trail, then they hack into the files of large corporations or individuals and steal. “This is increasing at an alarming rate,” says Harold M. Hendershot, an official in the FBI’s cyberdivision. “It used to be that hackers claimed to want to point out societal vulnerabilities – they actually claimed to be doing it for the benefit of society. But now more and more criminals are realizing that information is power, power is money, and knowledge is easy to get if you break into the right systems.”
The problem has been germinating for years. Identity fraud, in which hackers glean information from the Internet to get free credit cards and make deals under another’s name – displaced run-of-the-mill scams as the U.S. Federal Trade Commission’s top problem in 2001. Last year the FTC got 219,000 complaints, and expects a tenfold rise by 2005. Even more alarming is the spike in wire fraud, credit-card theft, stolen trade secrets and extortion.
How much money is being stolen? Estimates are hard because many victims – especially banks and other corporations – are reluctant to speak about their losses. By most accounts though, the problem is growing rapidly. Mi2g, a computer-security firm, puts the worldwide economic damage from digital attacks at between $37 billion and $45 billion in 2002. Other estimates fix the damage for 2003 at $135 billion. It’s no longer just Westerns being hit. According to one survey, 77 percent of executives at Brazil’s largest companies reported problems with cybercrime security in the past six months, up 43 percent from the previous year. In Russia, computer-related crime cost Internet users an estimated $6 billion in 2002 – triple the year before.
It seems odd that Internet crime would have risen steeply since the September 11 attacks, when security became a priority for most organizations. Criminal gangs, it seems, have only just begun to realize how much money can be made. They’re either learning how to hack the Internet themselves or are recruiting ambitious young hackers to do their dirty work for them. The Internet is reaching more of the world’s have-nots, tempting them to turn it against rich Western corporations. In January, 59 million Chinese used the Internet regularly, a 2,800 percent rise from 1998, according to the China Internet Network Information Center. Although that’s a fraction of China’s 1.3 billion people, the country has already become one of the fastest growing hacker havens. Russian hackers for hire complain that their Chinese counterparts are driving down prices for their services, by charging 10 to 50 percent less.
The result is a growing onslaught on legitimate Internet users. The average U.S. company is now attacked 30 times a week, according to security firm Symantec Corp. Most are efforts to scan for vulnerabilities, but about 15 percent are actual attacks. The number of Web-site violations reported to Carnegie Mellon’s Internet-security center jumped to 114,855 this year from 82,094 last year. The number of software holes reported in the nation’s computer networks grew by 80 percent in 2002, says Symantec. “There is a cat-and-mouse game going on,” says George Bakos, security expert at Dartmouth’s Institute for Security Technology Studies. “Unfortunately we would fall into the category of mice: we’re the target. The hackers keep coming up with new ways to go after us.”
Alexey Ivanov is typical of these new hackers. He began fooling around on computers at the age of 7 and scored at the genius level on intelligence tests. But there isn’t much opportunity in Chelyabinsk, Russia, a depressed area of the Ural Mountains, even for a computer whiz. Ivanov dropped out of college because he couldn’t afford the tuition and got a job as a furniture mover. He “recognized the obvious, that [his furniture-moving job] was a dead end and a complete waste of his professional-level skills with computers,” says his attorney, Morgan Rueckert. So in the spring of 2000, Ivanov joined a team of other computer experts and set to work hacking corporate Web sites. New servers have passwords that are set by default at the factory, and some corporations don’t bother to change them. Ivanov knew the passwords for Microsoft NT servers, and would scan the Net for vulnerable servers. When he found one, he’d hack in to steal credit-card numbers.
Ivanov and his cohorts quickly moved on to more sophisticated scams. Using a practice called “spoofing,” he created a Web site he called “Pay Pai” that looked exactly like Pay Pal’s site. Then he and his gang would send e-mails to Pay Pal users telling them to contact the site to collect credit, and offering a link to the Pay Pai site – where they’d enter their credit card numbers. Such attacks, known as “phishing,” are common nowadays – 18 banks in Australia, New Zealand, the United States and Great Britain have been hit in the past six months.
Computer viruses have become a standard tool of hacker criminals. Hackers send them out to infect vulnerable computers, turning them into “zombies” that can then be manipulated to launch attacks, or using the Trojan horse viruses that surreptitiously cull credit-card data, passwords or other sensitive information. Just like the mythical equine of old, a hacker horse usually comes as an e-mail attachment masquerading as something tempting, such as “sex.movie.mpg.” Opening the attachment activates a program that gives the hacker access to the contents of the infected computer and the ability to control it. Last month in Brazil, police arrested 28 hackers in four states who had stolen more than $10 million using a Trojan horse disguised as a “You’ve Just Won a Trip” promotion.
Hackers have lately begun to exploit fear to extort money from would-be victims. Ivanov and his team used this technique to blackmail Web-site owners from Seattle to Connecticut, threatening to expose their security vulnerabilities if they did not wire cash to Russia. In a spate of recent cases, criminal gangs overseas have begun threatening to launch distributed-denial-of-service attacks (DDS), flooding a server with so much incoming data that it crashes. In September, more than a dozen offshore betting sites serving the U.S. market were reportedly brought down by DDS attacks. The attackers then followed with e-mails demanding payments of up to $40,000 – though extortion schemes can run as high as $500,000. The Financial Times reported the investigators, who traced the assaults back to St. Petersburg, believe the Russian mafia was running the show.
Indeed, there’s increasing evidence that organized crime is moving in on Internet crime. Ivanov and his confederate Sergey Gorshkov were known to be attached to a sophisticated criminal ring. They reportedly paid 30 percent to a guardian, who oversaw a loosely knit network of hacker criminal cells. In Italy, considered a major hacker hub, “there are strong rumors that the Italian mafia is directly involved,” says Dario Forte of Italy’s elite Guardia di Finanza. Brazil has also long been a breeding ground for organized-criminal gangs, who take advantage of lax laws. According to mi2g, 18 of the world’s 20 most active hacking groups are based in Brazil.
The foot soldiers of these cybercrime gangs appear to be either young, precocious kids or frustrated men in their 20s or 30s. They’re increasingly likely to hail from developing countries with rampant unemployment, and to see their computer skills as a ticket to opportunity. Most of them are probably recruited by criminal groups through Internet chat rooms. One South Korean crime group held a bogus hacker contest and recruited from among the more promising contestants. By the time Korean police busted them last month, their ranks had swelled to 4,400 hackers, who had broken into the Internet servers of more than 90 government offices and private firms and stolen the personal information of more than 2.6 million people. All told, hacker crimes have soared in Korea from 449 in 2000 to 14,065 last year, according to the National Police Agency.
So why can’t law enforcement stop cybercrimes? For one thing, hackers are elusive. Just as Mafiosi will launder money to disguise its source, sophisticated cybercriminals disguise their origin. “If I’m going to hack your system in New York, I would probably hack into four or five systems worldwide first to disguise myself,” says the FBI’s Hendershot. “I would pick countries where I know the laws aren’t as great to investigate crimes, or maybe [the United States doesn’t] have the best international relations.”
The FBI grew so frustrated with the lack of co-operation with Russia’s cybercops, it resorted to desperate measures to nab Ivanov. Through a phony computer-security company in Seattle, FBI investigators asked him to fly there for a job interview. Ivanov jumped at the chance to escape Russia, even offering to bring his cohort Gorshkov. When the pair arrived, they put on a computer-security demonstration for the undercover cops, using tools from their own Web sites back home. This time, it was the FBI who captured Ivanov’s and Gorshkov’s keystrokes, brought into their computers and downloaded evidence. The hackers had been hacked.
The FBI may have nabbed Ivanov and Gorshkov – Ivanov is serving his jail sentence near Hartford, Connecticut, having pleaded guilty to hacking into 16 Web sites and attempting to extort money; Gorshkov got off with a 15-month sentence – but the conviction came at a price. The Russians were furious at the stunt. They accused the FBI of illegally obtaining evidence and indicted the agents working the case of crimes in Russia. The FBI recently offered $100,000 for hardware, software and training to Russian agents, but they are unlikely to make much headway against the hackers. Hacking into U.S. systems isn’t illegal in Russia. Ivanov’s crime ring is still believed to be intact.
The lack of antihacking laws is not unique to Russia. China’s laws regarding cybercrime are inadequate, say officials. Brazil’s legislation provides for paltry incarceration rates and enforcement is lax. The EU has drafted laws similar to those in the United States, but has yet to ratify them. In Hendershot’s opinion, only the United States and Britain have laws that come even close to adequate in defining cybercrimes and leveling penalties.
What can companies and home-computer users do to protect themselves? Vigilance is the only option. Corporations – particularly small- and medium-size ones – could do better at availing themselves of new software that plugs security holes in antiquated servers, such as new products introduced last year to deter certain kinds of spoofing scams. And whereas large corporations generally hire security experts to scan their software and computers to make sure that any backdoor administrative passwords are deleted, most small- and mid-size companies don’t bother. Individual computer users can be even more vulnerable. “There are so many industry-best practices not being implemented by home users,” says Dartmouth’s Bakos. Among the recommended practices are using firewalls and security software. Says Lee Byong Ki, police chief in charge of cybercrimes in South Korea: People “need to understand that as soon as their server is connected to the Internet, their information is exposed to hacker attacks.”
In retrospect, it seems naïve to expect a network of networks, designed not for security but to open to all, to remain free of the criminal element for very long. Almost from the beginning, the Internet has embraced the good and the bad, the inspiring and the mundane. Perhaps it’s only natural that criminals are at last taking up a place, too. How long it will take for law-makers and police to catch up with them is anybody’s guess. But when they do, the Internet is apt to be a much different place than what it started out to be.
Adam Piore
/Newsweek, Dec.22, 2003/